What exactly is TPRM?
| By The Mirato Team
An Introduction to the World of TPRM
In a “red ocean” business environment, where there is ever-growing pressure to innovate and outperform the competition, global organizations can be at great risk. This is due to the strong momentum that forces them into using third-party services to fulfill their operations and reach their goals. However, there is a risk in relying on third parties because doing so may hide a real threat: They can be revealed as an Achilles’ heel to a business’s security and/or reputation in different business domains. After all, your organization can be 100% secure internally, but if a business partner suffers a breach, your organization’s reputation, data and operations can also be at risk. As such, Third-Party Risk Management (TPRM) is becoming a top priority for CEOs, on par with innovation, efficiency and productivity.
This article will provide an overview of TPRM and why it’s vital for businesses today to not only incorporate this practice but prioritize it in their operations. TPRM does more than enable companies to remain competitive, it ensures their surival. Keep reading to learn more.
What exactly is TPRM?
TPRM is the process of assessing ongoing risks associated with using third parties that are presented to an organization, its data, operations and finances. In the realm of TPRM, third parties are defined as any legal entity that a company does business with, either in the upstream or downstream level of the supply chain. They may include suppliers, vendors, contract manufacturers, software providers, business partners and affiliates, brokers, distributors, resellers, and agents.
For example, a hurricane is forecast to hit South Texas three weeks from now. A big railway company wants to know what the probability is that one of its third-party iron suppliers will be harmed and, if so, what the possible impact will be. Meaning, what is the risk that the railway company faces? Is there a chance that they will only be able to get 50% of the metal promised to them from this third party for the next three months? Or, is the worst case scenario 10% of the metal for one month? The railway company needs to know how high the probability is for any of these scenarios to take place.
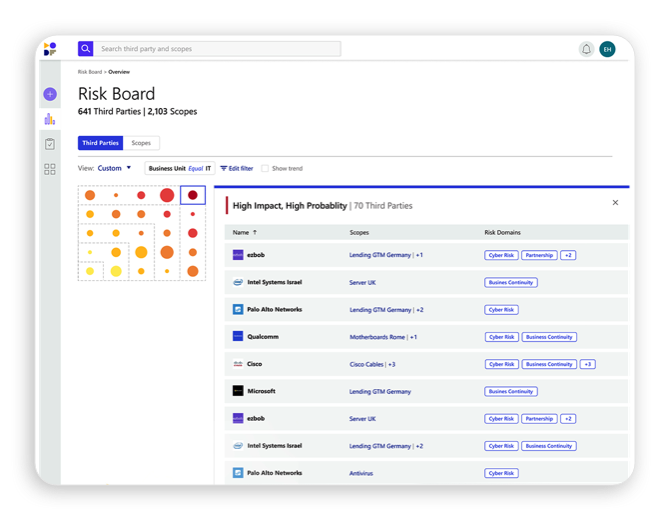
As the above example shows, in order for a company to manage the risk involved in working with third parties, it first needs to be able to define and assess the potential risk and its impact. In TPRM, risk is defined as the combination of the probability that something will happen and the impact it may have. As any business knows, there is potential for risk in any type of interaction, transaction, contract or relationship it has with a third party. These areas of cooperation where risk may surface are referred to in TPRM as scopes, or scopes of work. For instance, a scope may focus on a: product, service, outsourcing, partnership, JV, M&A, investment and/or donation between two legal entities. Each different scope – and the amount of money involved – will then determine the type of risk assessment needed by a company’s TPRM analysts or platform.
Probability & impact are the name of the game
There are two factors that determine the level of risk: probability and impact.
Impact – What might be the impact, or damage, of the potential risk? How is it going to affect the third party’s ability to provide its product(s) or service(s) to the assessing organization?
Probability – What is the likelihood that a scenario will happen that will cause direct or indirect/causal risk and/or harm to the company?
Let’s revisit the Hurricane in South Texas example. The railway company still wants to know whether any of its suppliers will be harmed and, if so, in what way(s) that risk will affect the company itself. Companies like Mirato offer a TPRM platform that allows companies to review each of their suppliers and third parties in real time to see which of them may be affected by a potential event (like the Hurricane). Using machine-learning-based NLP models and sophisticated data harvesting, it provides an ongoing risk visibility that the company can act upon.
Types of risk domains
With limited opportunities for growth in traditional ways, businesses are turning more and more to digital approaches and strategies to grow revenue and to reach a wider segment of customers. CEOs recognize that a greater focus on digital means more danger to their businesses. Third-party risk assessment and management entails creating a clear picture of a company’s partners in various business domains. The main risk domains covered by TPRM include the following:
- Cyber – This comprises any risk that is related to financial loss, damage or disruption to an organization’s reputation that is a result of failure in or erroneous or unauthorized use of its information systems. The digital revolution has had a huge effect on banks, as well as everyone else
- Data Privacy – This represents the potential for a loss related to your data. The term applies to failures in the use, storage, transmission, security and management of either personal and/or company data.
- Physical Security – This is the safeguarding of software, hardware, networks, personnel and data from physical events and actions that could potentially lead to serious damage or loss to a company, enterprise or institution. Examples include protection from flood, fire, natural disasters, theft, burglary, vandalism and/or terrorism.
- Business Continuity – Also referred to as business continuity planning (BCP), this involves putting a system in place that helps a company prevent potential threats and recover from them.
- Financial Stability – This term refers to when the overall financial system, including financial markets, is stable and resilient to any unexpected or potential economic shocks. This state of stability ensures that the financial system is able to manage and see through its functions, which entail overseeing and enabling the flow of financial funds, arrangement of payments and the management of financial risks, among others..
- Geographic Resilience – This term is essentially interchangeable with “disaster resilience,” as the latter and its associated disasters, hazards and risks, are geographic in nature. Both types of resilience are defined by the interaction that occurs between loss and social and biophysical response. Simply put, geographic resilience is when a response is timely and effectively implemented, it reduces the loss and ensures a higher level of resilience.
It’s important to note that all of these risk domains are very subjective. This means that individual organizations, businesses, enterprises and banks will most likely have a different definition of each domain for their respective TPRM processes. For example, one bank may have six huge risk domains while another one has 15 smaller risk domains.
The 5 Stages of TPRM
When it comes to the actual TPRM process, there are five main steps, according to the Office of the Comptroller of the Currency (OCC), which is an independent branch of the U.S. Department of the Treasury. The OCC regulates and supervises all national banks and federal savings associations as well as federal branches and agencies of foreign banks. In other words, the OCC is more or less the industry watchdog when it comes to third-party management. They break down TRPM into the following 5 stages (more or less):
- Planning: (What are the risks involved in acquiring the service from a third party as opposed to doing it internally?)
- Due Diligence and 3rd-party selection: (Doing due diligence on all potential third party options and then selecting the party accordingly.)
- Contract negotiations: Using the data from above for contract negotiations.
- Ongoing monitoring: Ongoing risk management and monitoring of vulnerabilities. Did the third party deliver on all promises and promised features?
- Termination: Once the scope of work is complete.
Not a recommendation, litigation
Today’s regulatory environment is complex. New regulations are constantly being introduced or updated that require more accountability from organizations with regard to better understanding and managing third party risk and its implications.
For example, EU countries introduced the GDPR regulations to uphold privacy in the digital age. Companies must meet these regulations or be held accountable. California is the first country in the US to adopt their legal framework and created the CCPA regulation.
While compliance is imperative, there is a genuine motivation for organizations, especially banks, today to prioritize and invest in state-of-the-art TPRM systems. This motivation stems from wanting to learn from and prevent others’ experiences with severe reputational damage caused by third parties (think extended fallout from Harvey Weinstein, the 2013 Target data breach, the 2016 Dyn cyber attack, etc). Having a TPRM system in place ensures that your organization will be on top of the necessary data it needs to define, assess and prevent risk, or else be prepared to handle any damage that arises should things go wrong.
Unlimited potential
Thanks to the digital revolution, which has had a huge effect on banks and everyone else, TPRM has extended as a necessity beyond procurement departments to operations departments, too. As the business and banking worlds – and everything in between – have evolved, so too has the field of TPRM.
In today’s fast-paced increasingly competitive business climate, an efficient TPRM program is not only an invaluable asset but a vital one. It enables businesses to quickly respond to – and keep up with – rapidly changing market dynamics. It also helps speed up important yet slow processes, like vendor onboarding, in a potentially more secure way. The best way for companies to operate more intelligently when it comes to risk is to be better prepared for it. For this to happen, it is beneficial to adopt a harmonized framework to hone innovative risk-assessment capabilities.

